SEO Guides, Tips & More!
Learn from Our Experience
Protecting WordPress Sites Against Cyberattacks
Data breaches, hacking, malware, phishing and social engineering hacks, ransomware, and other types of cyberattacks are rampant. Attention to cybersecurity and the growing threats of online attacks is only going up. And accounting is far from being spared:
- Late last year, Top 20 firm Moss Adams disclosed a data breach that exposed an unknown number of client names and Social Security numbers.
- In the spring of 2019, Wolters Kluwer experienced a malware attack that took down its entire software suite.
- In 2017, Deloitte suffered a cyberattack that put an undisclosed amount of client information at risk.
Compounding the issue is that current estimates report that only about five percent of companies’ folders are protected against cyberattacks. It’s not just large accounting firms that are at risk; the majority of “easy targets” are small to mid-size firms that may not have the depth or scope of security and IT protocol to protect against cybercriminals. Considering that accounting firms maintain a substantial amount of personally identifiable information, they are extremely vulnerable to online attacks.
In at least one of the above cyberattacks, email was the means of opening up the data breach; however, websites are prime targets for hackers to inject ransomware into the system and cripple firm servers.
WordPress powers around 30 percent of the internet’s websites, so the number of cyberattacks against WordPress sites is correspondingly high. Read on to learn about:
- Potential cyber threats via the website,
- Common areas of WordPress vulnerabilities, and
- Ways to increase WordPress site security.

Potential WordPress Cyber Threats
Malware is among the most prolific website threats and includes viruses like spyware and ransomware. Viruses can damage an entire computer system and all the files in it. Spyware is one of the more common viruses and operates in the background, without the user knowing, to observe information like log-on credentials, account numbers, and more. No matter the kind of malware, all types rely on human users to take some sort of action to initiate the cyberattack.
One of the most dangerous ways a hacker uses a website is to put a ransomware file onto the server.
Ransomware is a form of malware. It is a malicious code that locks up the computer and/or server files, usually followed by a demand for money to regain access. Ransomware attacks are more common through email, but this type of malware can attack websites in a number of ways, especially by downloading plug-ins or videos from unofficial sources. EV ransomware is a newer form of ransomware specific to WordPress.
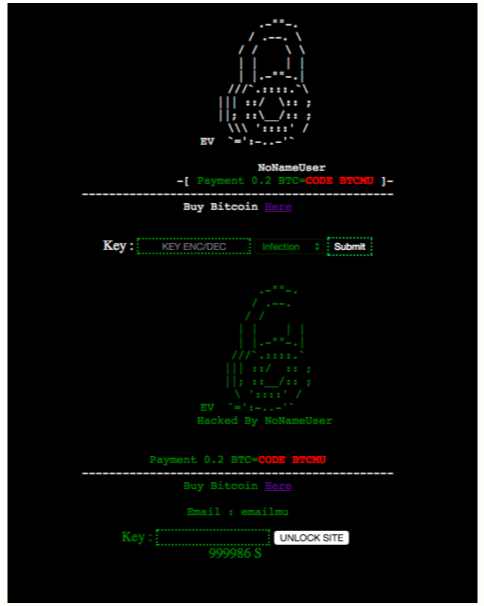
If a site is compromised by EV ransomware, the log-in screen will look something like this, courtesy of Constant Contact:
dDos, or Distributed Denial of Service attacks, target servers or private networks. They disrupt regular internet traffic to a site or server, thereby preventing anyone from accessing it. Firms with connected networks, such as security cameras and remote networks, can be especially vulnerable to dDos attacks. Marketers and CPAs who want to read more about the types of dDos attacks can do so here.
Security Flaws in WordPress Sites
WordPress has thousands of plug-ins that allow web developers and managers to customize the site. The problem with this is that plug-ins can open up vulnerabilities in a site. Unless they’re frequently updated, third-party plug-ins are a leading cause of attacks against WordPress sites.
Outdated WordPress versions, themes, or PHP versions are other areas of potential security flaws. Every WordPress site should be running the latest theme and core version of the software. Some web hosts will update these automatically, but many accounting firm marketers end up doing these types of web updates manually.
Weak passwords create another area of vulnerability. Cracking is the process of hacking the WordPress password using a sophisticated (or sometimes not so sophisticated) computer program. Brute-force attacks attempt random combinations of characters based on identifiable information, like names. Dictionary attacks attempt to combine millions of different combinations in a short amount of time.
A giveaway of an attempt to hack the password of a WordPress site is being locked out for no apparent reason. And once the password to a WordPress admin site is discovered by a hacker, the entire site becomes vulnerable.
Use of email, or phishing attacks, to hack websites can be done if a hacker pretends to be someone who needs the password to the site, like someone posing as the developer or web host. In a smaller site, this won’t be much of an issue; but larger sites with multiple users could be open to phishing attacks like these.
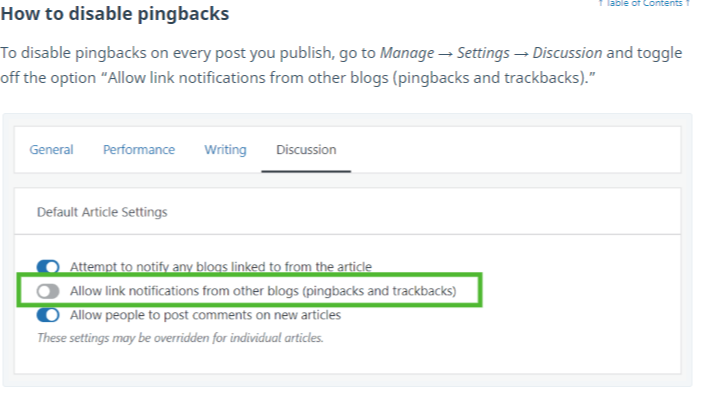
Other common access points for hackers are unsecured networks and failing to disable pingbacks, in which one blogger links back to his or her site in blog comments.
Ways to Increase WordPress Site Security
WordPress sites are inherently safe, but all websites are susceptible to cyberattacks. That’s why it’s important to take proactive steps as a website manager to keep all site assets safe.
Perhaps one of the most important security considerations to protect websites is the web host. All the protective measures in the world won’t stand up well if the back-end hosting and administration is lax. The best web hosts will have built-in security features to minimize the risk of web hacks or the need for extra plug-ins.
Things to look for from a secure web host:
- Restricted access to servers and hosting infrastructure
- Regular network monitoring for unusual or unauthorized activity
- SSL and firewall encryption – an SSL encryption protects the website data, whereas a firewall protects the network
- DDos prevention tools (there are several to choose from depending on the host, server, and site)
- Malware detection tools
- Automatic and frequent backups; offsite backups are best for large sites
The log-in screen is the first place hackers will try to gain access to the site. Implementing a variety of security measures here can go a long way in protecting the entire site. Consider:
- Setting an extremely strong and unique password
- Limit log-in attempts
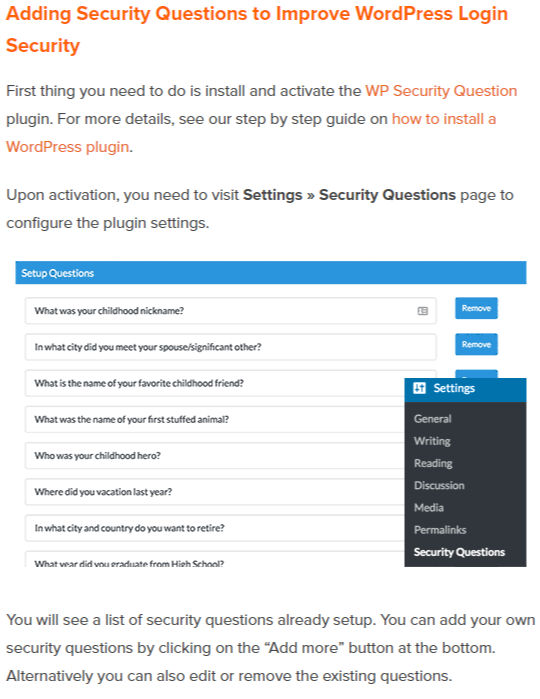
- Require two-factor authentication, like security questions
- Automatically log out idle or inactive users
- Manually log out of each session when finished
Outdated PHP files are another source of frequent WordPress attacks. Work with the developer to update PHP files and disable file editing and PHP file execution. It’s also a good idea to password-protect admin usernames and passwords within the back-end interface.
For larger sites with multiple users, consider implementing training on phishing and other types of cyber-attacks – for website users and anyone in the firm, really. As the saying goes, an ounce of prevention is worth a pound of cure, and phishing training is less expensive and time-consuming than buying a year’s worth of credit monitoring for all the firm’s clients.
Finally, ensure the site has appropriate security plug-ins installed. The right plug-ins can actively monitor and protect against potential threats, scan for malware and other malicious activity, enable firewalls, and more – as long as they’re up-to-date. On the flip side, uninstall plug-ins that aren’t being used anymore.
Look for more content on the Flashpoint blog to help protect WordPress sites, like:
- The impact of security breaches on website reputation and search performance
- Types of hackers, what they’re after, and how to protect against each one
- Top WordPress security plug-ins
- What to do after your WordPress site is hacked
Is there a security topic you want to learn more about? Tell us in the comments.

